ERP Cloud Security and Audit: Proven Best Practices
-
Posted by Quest Editor
- Last updated 4/02/26
- Share

ERP Cloud Security and Audit: Proven Best Practices
When you are getting started with any type of enterprise application, you expect to plan security of the application, achieve that level of security during the project, and then ensure ongoing security after go-live. In terms of methodology, the first step of planning deployment could look similar to the following image:

As a glossary of terminology for ERP Cloud, HCM (human capital management) Cloud, and SCM (supply chain management) Cloud, the action starts with each user having an account. The user logs in to the cloud. The user account can give the user the ability to log in. The role can specify the ability to do and see. Together, roles assigned to the user account give the user the ability to do and see.
Configuration of Roles
There is a consistent pattern in ERP. First, the configuration of roles occurs. Then, a user account is created. Next, roles are assigned to the new user account. Finally, it’s go-live. Often, there is another step that occurs months later when an auditor steps in to ask:
- What can the user do?
- What roles could they let users do and see?
- What are the assignments of the roles letting users do and see?
Unfortunately, the answers to these questions are not readily available in most cases.
The challenges in choosing how to secure applications show up in the following statements:
- “I’m not sure how to design roles or assign them to users.”
- “I’m not sure what users can really do.”
- “Access certification is laborious.”
- Auditor says, “Access controls must be stronger.”
The on-ramp to a secure ERP is a three-step process:
- Define controls: Determine what users should not be able to do.
- Tune roles: Balance business performance versus risk reduction.
- Certify: Ensure that users can do what they should and not what they shouldn’t.
To define controls, you must determine what users should not be able to do. The categories that this can be broken into are:
- Separation of duties
- Access to restricted data
- Access to unnecessary functionality
One example of separation of duties would be to separate the abilities to create a supplier and pay the supplier. As for accessing restricted data, data belonging to a different region or personally identifying information should not be accessible to the user. Finally, access to unnecessary functionality comes into play as users promote or change responsibilities. The user should not retain the residue of past roles. For instance, a payable administrator does not need inventory management abilities.
Tuning roles begins with prebuilt roles. As you work with the prebuilt roles, risk management allows you to do live analyses to determine what the roles are letting the user do.
- Begin by assigning one role to a test user.
- Analyze access for the test user.
- If too permissive, use Security Console to modify access.
Role Assignment
The second step is to tune the role assignment. You’ll use the function called role mapping. You can create a role mapping for a user with a certain set of properties, such as a role that is needed by Payables Administrator for South America. Again, you can test the role mapping in Risk Management. Analyze the test user and adjust mapping, adjust roles conferred by the mapping, or use Risk Management to continually monitor transactions generated by users with SoD concerns if an analysis revealed SoD concerns.
Note: If roles are assigned by external automation such as Oracle Identity Cloud, use that automation’s functional equivalent of role mapping.
Before go-live and periodically, have your managers certify that any high-risk functionality is only available to the user that should have it. Focus on your risks and documentation expected by auditors. This is more efficient than typical certification. There is an automatic creation of certification criteria with Risk Management. You can automate workflow with Risk Management, replacing spreadsheets, reports, emails, and phone calls with secure worklists and intuitive worksheets.
When securing live ERP with HCM Cloud, SCM Cloud, or Oracle’s Software as a Service (SaaS), the same three steps apply. However, instead of defining controls and roles, you will review them. Then, you will re-certify with Risk Management.
Risk Management Cloud Customers run the gamut of industry, scale, and region. The image below displays a small portion of active subscribers.

Personally Identifiable Information
As far as personally identifiable information (PII) goes, the Risk Management app allows you to find all the access points within the fusion security cloud for users with access to PII privileges. Risk Management has the capability of accessing all the fusion security layers to be consumed in the application. The image below shows a blow-up of the access points with PII and the examples of abilities to access, manage, and change specific pieces of PII. This certification can be launched to reveal this information, as well as the chain of custody between the user and those fine access points.

This is an example of one of those reports.

Roberts created an example visualization to illustrate one of these use cases.

It can also be displayed as a spreadsheet.

When moving from design to implementation, certify users. Remove access to broad access points within live. Online certification capabilities can certify users against their roles.

Data Science of Risk Management
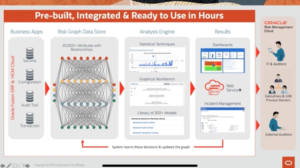
In Machine Learning, there is self-learning and guided learning. Self-learning has the virtue of requiring no human interaction. The downside is an enormous number of false positives and false negatives. Guided learning requires human interaction, but it can drive out false positives and false negatives to deliver the kind of results most needed in risk management. The slide below shows the flow of information and that the Risk Management internally understands what is going on in the applications, provides tools for taking advantage of and presenting that information, and guides the behavior of that analysis.
Another primary of data science is the application of statistics. While the first illustration showed graph mathematics, this slide shows statistical mathematics for the purpose of solving business problems. Actual data sets of numbers tend to have a certain distribution of leading digits. Any time there is a data set with significant variance from the expected pattern, there is probably something to look at and drill in. This is one forensic accounting technique that relies on statistical tools available in Risk Management.

Key Takeaways
Risk Management can be a huge asset to your organization’s security. Leverage the security and audit tools to assign roles, analyze access, and modify necessary permissions. Take a closer look at your Personally Identifiable Information to protect your company and your customers. Review SoD with security analysis tools and monitor high risk changes to master data and cloud application configuration setups. These tools are available as part of ERP Cloud, HCM Cloud, and SCM Cloud.

